RAID Logs
Every project comes with a whole range of risks, issues, assumptions and dependencies, which depending on their severity, can make or break a project. When you have hundreds of projects in your portfolio, managing these items can quickly become a real costly problem.
How pmo365 helps with your RAID Logs
With pmo365 you can store and update your RAID logs in a single centralised location that gives your organisation maximum visibility and control to all your projects. Even more, all this data will be ongoing and in real-time so you can make strategic interventions and revision as quickly as possible.
If you want to find out how exactly we accomplish this for your organisation, keep reading on.
What are RAID logs and why are they important for my organisation?
RAID logs are a project management tool that enables all managers to log, document and track the Risks, Assumptions, Issues and Dependencies associated with a project. There are a few variations of the acronym for RAID, some that add or interchange factors such as Action and Dependencies to form the extended RAID. We’ll elaborate on these categorisations further down.
RAID Logs are incredibly useful for your organisation as they essentially act as a shortcut for major stakeholders that consolidates all key reporting elements in one place and allows for streamlined communication, organisation and intervention of on-going risks.
This increased visibility also gives organisation control over their projects as they can step in before risks become too large. RAID logs are also the simplifying framework through which your organisation’s risk management strategies can be properly executed across all levels of the organisation.
What are the categories of RAID Logs
RAID logs have different category configurations which can be adapted and altered depending on how best they suit an organisation’s activities. These categories include:
Risk
Risks are potential problems that may occur as the project progresses. Risks can impact pretty much anything - from people to processes and technologies. Though risks are typically associated with having an adverse impact on a project, in rare cases there can also be positive risks. It is important to differentiate risks from issues. Risks are potential problems while issues are present problems.
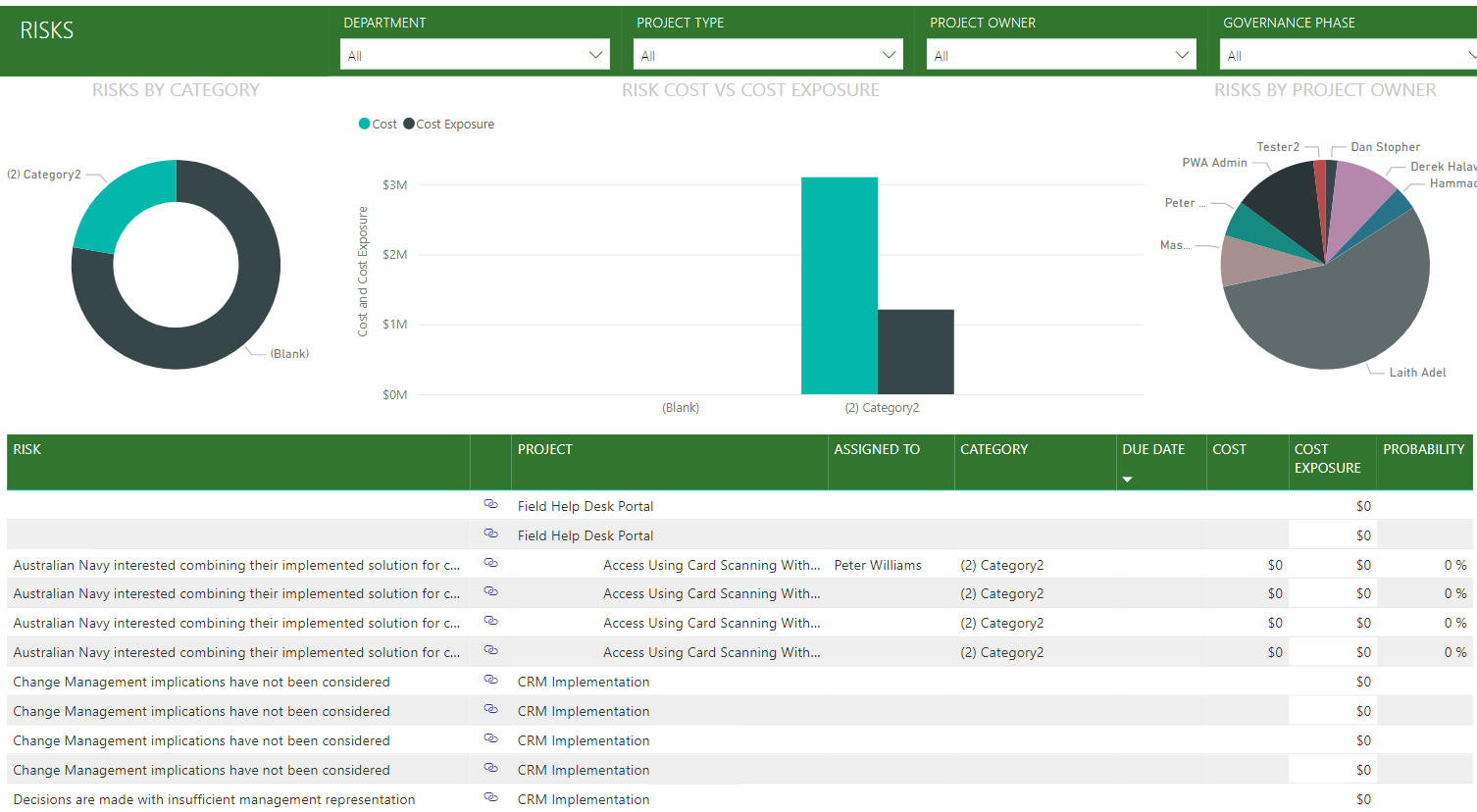
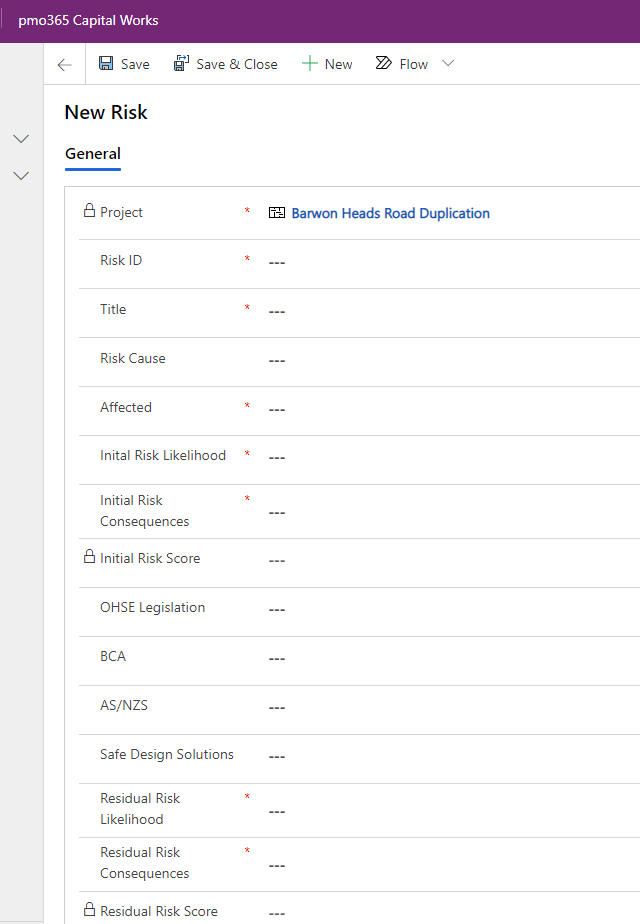
Below are screenshots of how your organisation can capture, manage and have visibility and control over all your projects portfolios risks in one place in pmo365:
Issues
Issues are problems that are present, currently identifiable and can or must be immediately addressed. Issues, when left unaddressed, can often escalate and potential derail a whole project or program.
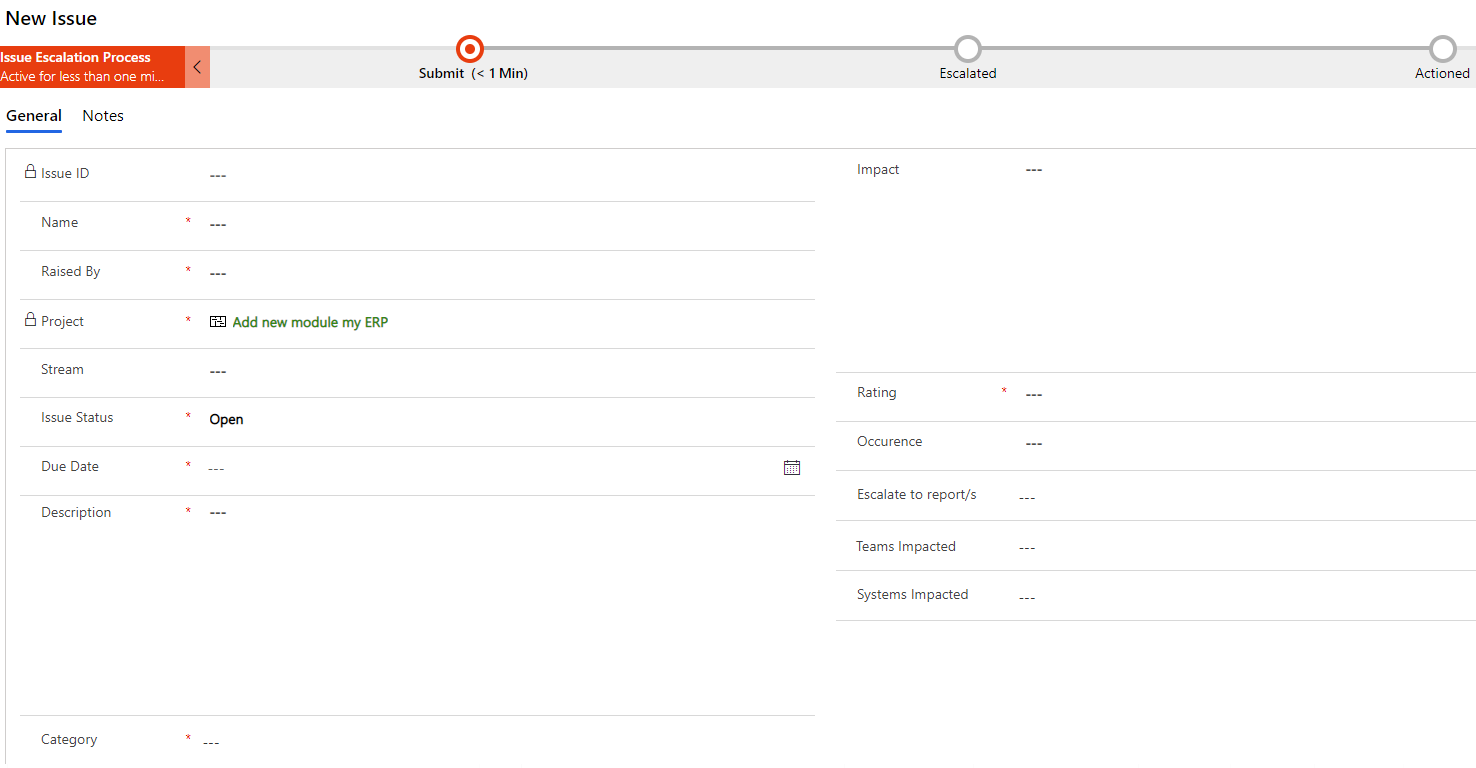
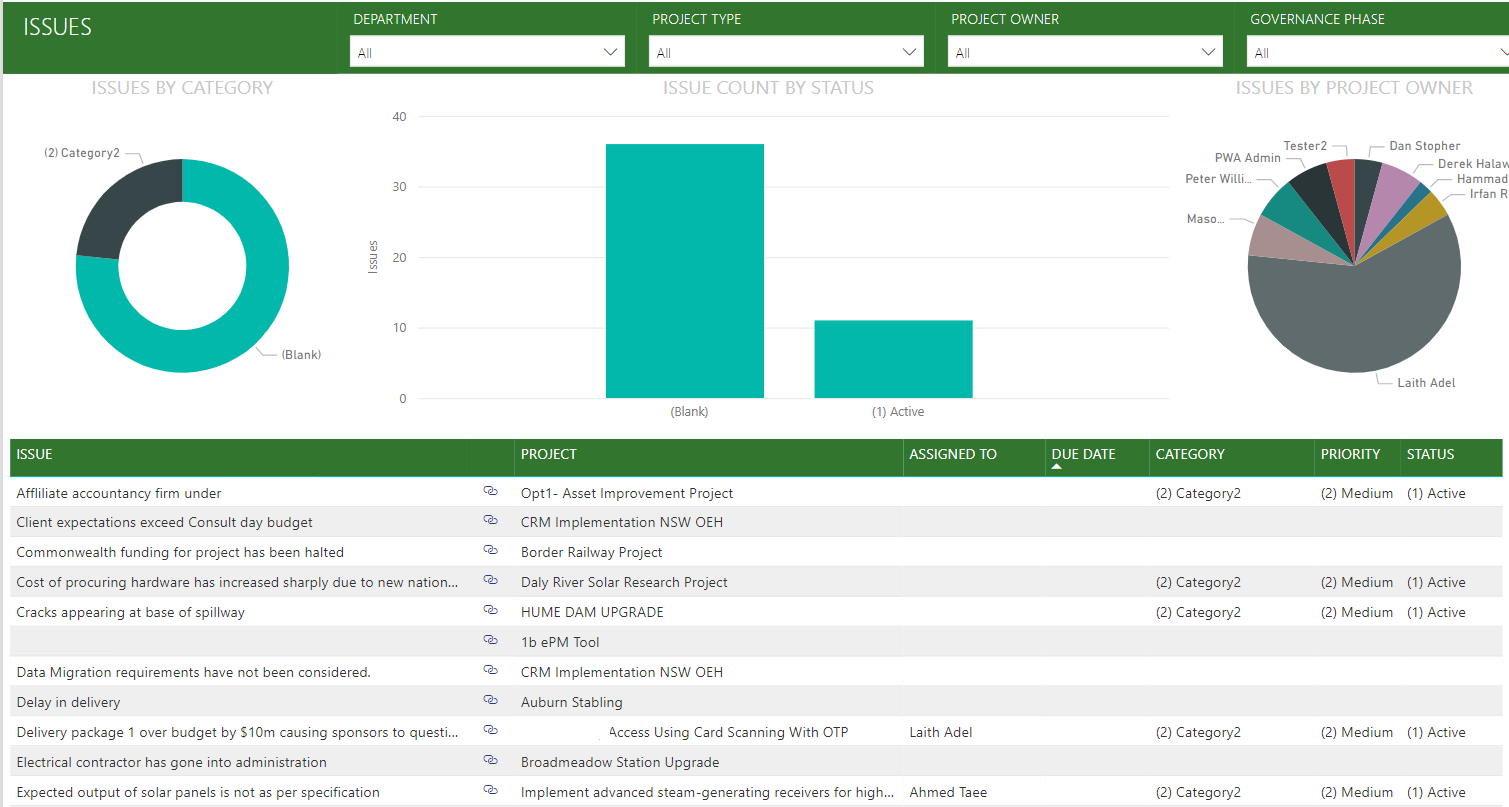
Below are screenshots of how your organisation can capture, manage and have visibility and control over all your projects portfolios issues in one place in pmo365:
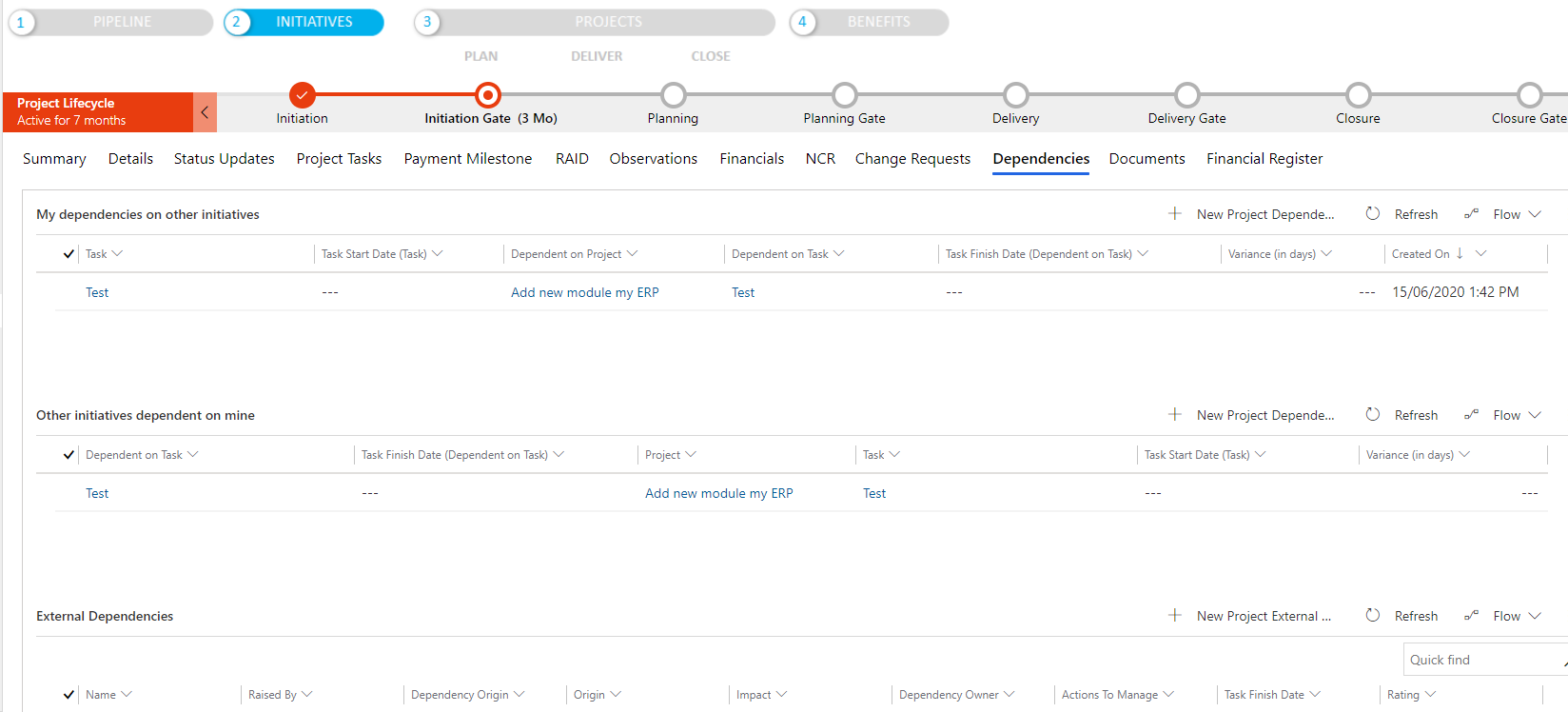
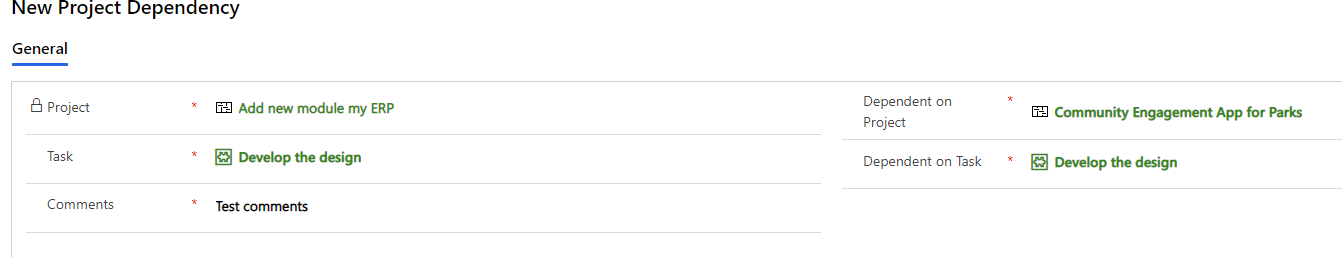
Dependencies
Dependencies are interdependent tasks that are critical to a project’s progression. There are several types of dependencies that must be identified to ensure they are addressed according. Dependencies can become issues if the tasks they are dependent upon are not completed leading to delays in overall project completion.
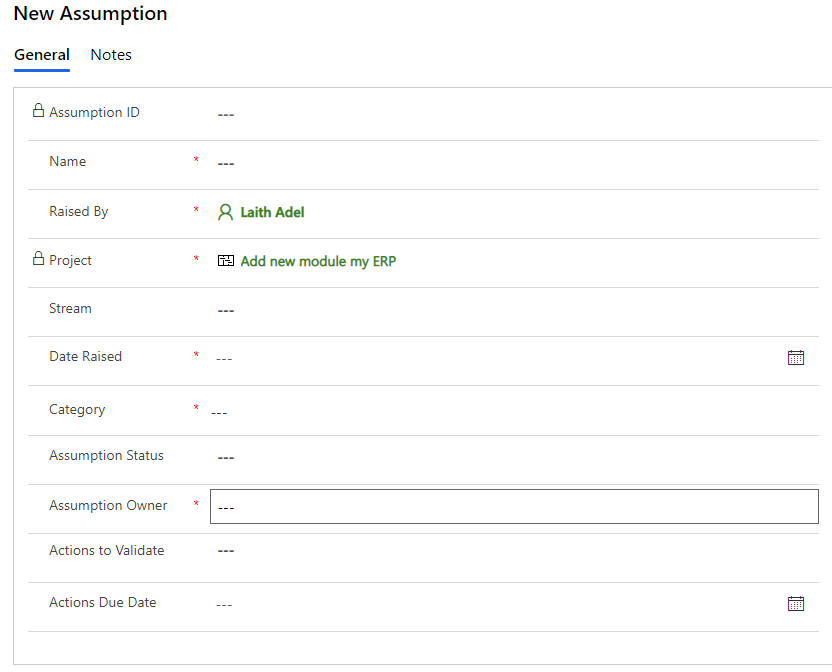
Assumptions
As much as we would like to hope every single action in a project is supported by empirical proof, most of the time that is not the case - whether that be due to data and experience limitations. However, this problem can be mitigated by first identifying all the current assumptions of the project and continually updating this list as the project progresses and more information is made available.
For some configurations of RAID logs, the Assumptions is replaced with Action.
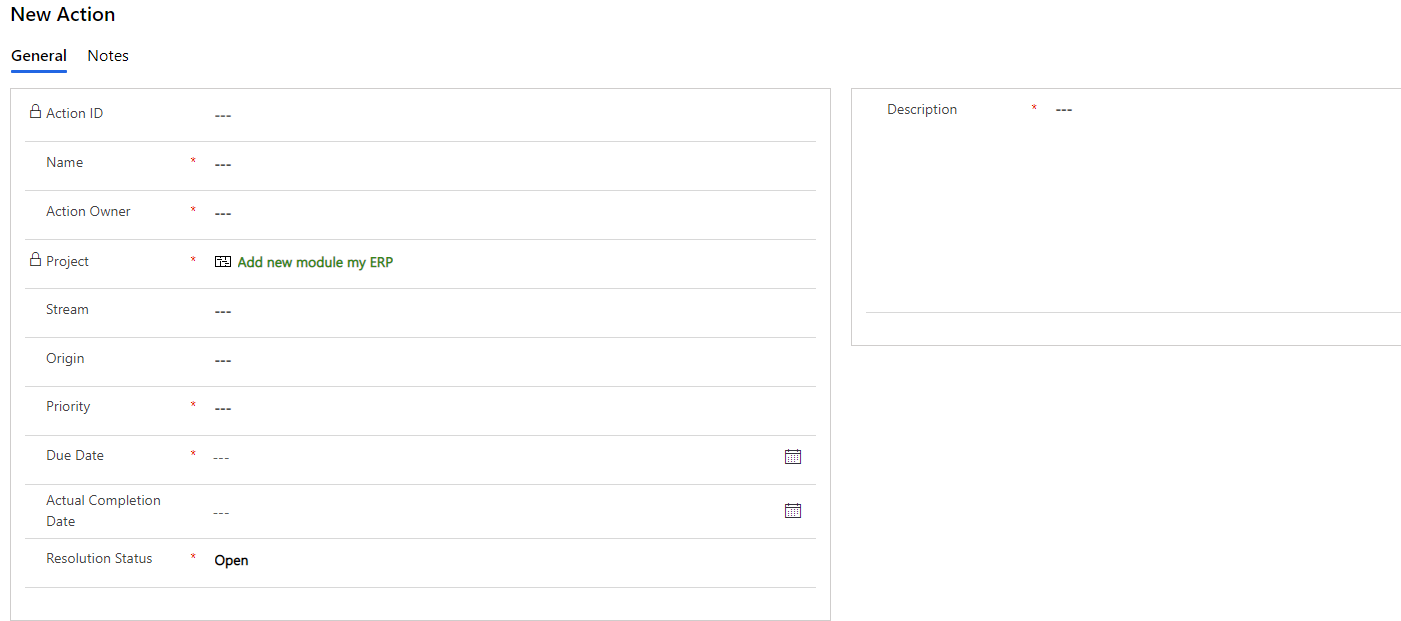
Action
Actions are activities that are aimed at mitigating a risk or resolving an issue. In most cases, actions are assigned owners who are then responsible for other more detailed activities that need to be done to address the risk.
In some configurations of RAID Logs, Dependencies can either be replaced or used alongside with Decisions.
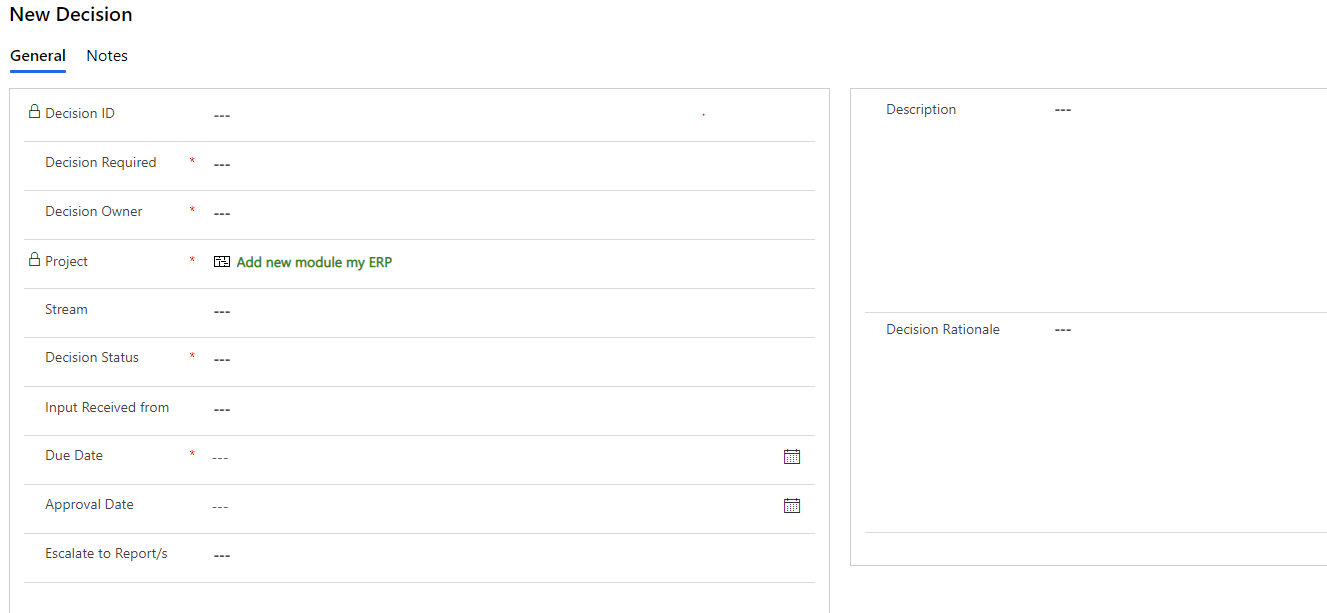
Decisions
The decisions category is used to list down the decisions that need to be made during the process of the project. This category aims to give a clear understanding of the thought process behind the project’s actions by defining decision ownership, accountability, justification, duration and execution.
How do RAID Logs work?
The first step is to select which categories you want to apply depending on your project’s contexts and needs. Don’t feel a need to have to apply all of them if unnecessary as you will end up with an overload or irrelevant information that takes up precious time and resources.
Once you have the categories defined, it's as easy as simply plotting everything down in a table or excel sheet like what has been done down below.
However, when you have hundreds of projects running, having people fill, input and edit endless excel sheets is not sustainable. At pmo365 we not only can give more in-depth information, we can make it all centralised with real-time data so you don’t have to work any harder to get even more valuable information. The added dimensions we introduce stem from risk management approaches and they help you identify the type of risk, attribute a risk rating and better implement risk response strategies. We’ll go into more detail below.
RAID Logs using Risk Management approaches
The three main risk management approaches that make for better RAID Logs are risk management’s risk types, risk rating (through a risk matrix) and risk response
Type of Risk
Risks can be categorised as two types: inherent risk and residual risk. These can be visualised in the form of a funnel.
Inherent risks
Inherent risks are the amount of risks that exist in the absence of controls or treatment to address it. These risks can be visualised at the top of a large funnel and will appear at the during the early iterations of the RAID Log at the beginning of the project lifecycle.
Residual risks
Residual risks are the risks that remain after the organisation has responded to the risks or issues raised in the RAID log. These can be visualised at the bottom of the funnel
Understanding the origin and characteristic of a risk will help give inform the level of impact it has over the project in the form of risk ratings
Risk Ratings
Risk ratings assess identified risks by classifying their impact on the business from low, medium to high risk. In some situations they are also given a numerical value usually ranging from level 1 (being low risk) to level 5 risk (high risk) and needs immediate action.
Risk ratings are often visualised in the form of risk matrix’s like the one shown below.
Risk ratings are a critical team which allows managers and key decision makers to effectively prioritise the risks and issues within their programmes and projects so resources can be allocated as effectively as possible.
Risk Response Strategies
With risks being more often negative than not, these are 5 of the most common risk response strategies.
Identify the Benefits
Avoidance
Avoidance responses aim to remove the cause of the risk itself. This often comes in the form of altering the scope of the project where this project originates. Though the easiest type of response, it is often the least applicable because of its large-scale impact across the entire project’s processes.
Acceptance
Acceptance responses acknowledge that certain risks are unavoidable and account them into the project’s plan. It is important to identify these risks from the very beginning of the project and that all relevant stakeholders are aware of these risks when they approve of the project and make future decisions.
Monitor and Prepare
This response is similar to an acceptance response but places controls to monitor the triggers that activate the specific risk and build action plans that can be immediately mobilised once the risk occurs.
Mitigation
Mitigation responses aim to minimise the impact of the risk or its probability of occurring. This response is often taken when early identification of the risk has been made and can still easily be mitigated before it escalates.
When managers and stakeholders have these frames of understanding risk responses, justification for decisions made can be clearer and solutions can be more easily structured.


Limitation of RAID Logs
The biggest limitation for RAID Logs often lies in the softwares they are built on. As previously mentioned, if an organisation does not have the proper systems and connectors, integrating all this information and automating its processes become increasingly difficult. Scale this up to hundreds of projects and it’s simply unmanageable and unsustainable.
This is where pmo365 comes to the rescue and is able to integrate all your data across different platforms in a centralised form so you don’t end up wasting valuable resources on menial activities like logging.
If you want to learn more about how pmo365 can streamline your organisation’s project management through RAID logs, book a free 30 minute PPM audit to speak directly with our PPM experts.
Our partners
We've worked with




AI Project Management Tools: All You Need to Know
.png)

Sustainability in Project Management: A Complete Guide
.png)

Project Financial Management Integrations with pmo365

